Introducing SIGHUP Distribution v1.34.0 latest release

We're thrilled to announce the release of SIGHUP Distribution version 1.34.0!
This release adds support for Kubernetes 1.34 and includes improvements in several areas, such as the adoption of a new ingress controller, kube-proxy-less clusters for the OnPremises provider, and the transition to OpenTofu.
Below are some highlights from this release:
- Support for Kubernetes 1.34.
- HAProxy Kubernetes Ingress Controller is the new reference ingress controller, following the official retirement announcement of Ingress NGINX Controller.
- The new BYOIC (Bring Your Own Ingress Controller) mode allows teams to use a custom ingress controller, not managed by the SD lifecycle.
- OnPremises clusters can now be deployed without kube-proxy, enabling Calico eBPF mode and Cilium's kube-proxy replacement to implement Kubernetes Service handling directly in the kernel.
- furyctl, the SD cluster lifecycle manager, now uses OpenTofu instead of Terraform.
- All core modules have been updated, including important security patches addressing several CVEs in Envoy and runc.
Note: this release includes breaking changes. Please make sure to read the relevant section in the official release notes.
Supporting Kubernetes 1.34
With this release, SD adds support for Kubernetes 1.34 over all distribution providers. While this upstream version does not introduce API removals or deprecations, it includes several enhancements. As part of our ongoing commitment to keeping the distribution aligned with the latest Kubernetes ecosystem, all core components have been updated.
Updated core modules
In this version, we have adopted HAProxy Kubernetes Ingress Controller (KIC) as the new default controller in the ingress module. This ensures continuity for Ingress resources in the SD after the announcement of the retirement of Ingress NGINX. Also all core modules have been updated including networking, monitoring, ingress, logging, tracing, policy, DR, and auth components.
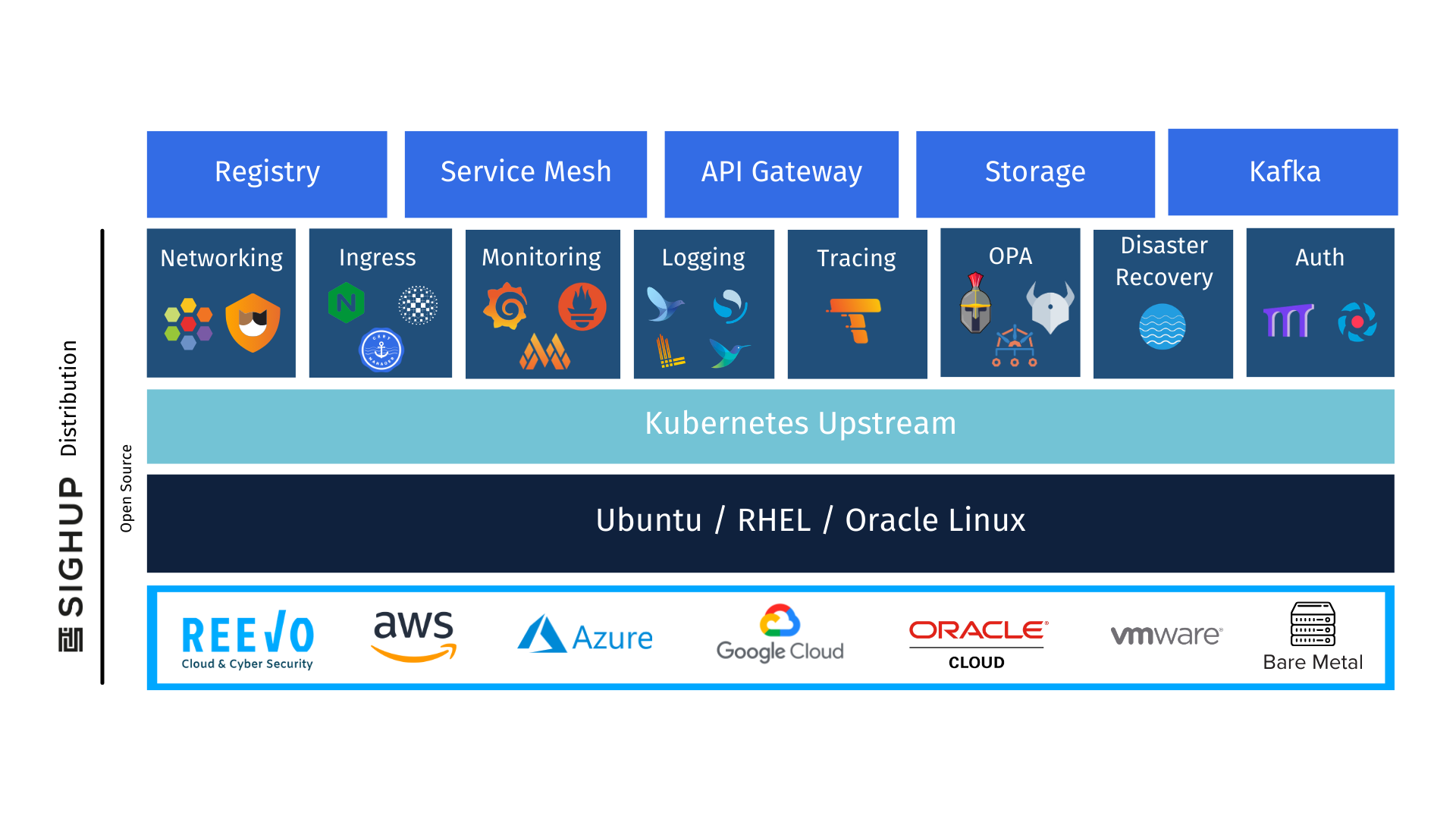
You can explore more about SD's modules here.
HAProxy KIC: the new reference ingress controller
We are introducing HAProxy KIC as the new reference ingress controller in SIGHUP Distribution.
The Ingress NGINX Controller project has been officially announced as retired by the Kubernetes community. While NGINX remains a widely adopted proxy, the upstream project has reached end of life as a Kubernetes ingress controller, which means no further feature development, and eventually no security updates. Continuing to rely on it as the default ingress controller would have exposed users to increasing operational risk over time.
HAProxy is a mature alternative that is already part of our distribution, where it has been used as an L4 load balancer in the OnPremises provider. Now SD supports both single and dual deployment modes for HAProxy KIC.
To ensure a smooth transition, the Ingress NGINX Controller is still supported in this release. For those currently using NGINX, we provide a migration guide: nginx-to-haproxy-migration.
We are also introducing BYOIC mode (Bring Your Own Ingress Controller). This allows teams to use a custom ingress controller deployed as a SD plugin or completely outside of the distribution lifecycle. This way you will have maximum flexibility when you have specific needs that go beyond the built-in options.
You can read more about the ingress module here.
Kube-proxy-less clusters
An important feature introduced in this release is the ability to deploy new OnPremises clusters without kube-proxy. This is a significant step forward for users who want to take full advantage of eBPF-based networking.
Kube-proxy is the traditional component responsible for maintaining network rules on each node. While it works well, it has limitations in terms of performance in certain use cases.
Disabling kube-proxy enables Calico in eBPF mode and Cilium's kube proxy replacement mode automatically in the networking module, giving you a faster and more observable networking stack.
You can disable kube-proxy on new OnPremises clusters with the following configuration:
apiVersion: kfd.sighup.io/v1alpha2
kind: OnPremises
metadata:
name: your-cluster
spec:
kubernetes:
advanced:
kubeProxy:
enabled: false
...From Terraform to OpenTofu
Another important change in this version is the replacement of Terraform with OpenTofu as the IaC tool used by furyctl under the hood.
As you may know, in 2023 HashiCorp changed the Terraform license, this change introduced restrictions that conflict with the open source principles at the core of SIGHUP Distribution. As a response to this change, the OpenTofu project was created as a truly open source fork of Terraform, maintained by the Linux Foundation.
Starting from this release, furyctl uses OpenTofu v1.10.0 instead of Terraform. This preparatory change unlocks new features that will allow us to evolve our EKS provider to introduce further improvements in the future.
Disaster recovery: GCS backend and new Velero feature
The DR module keeps getting more flexible. This release adds support for Google Cloud Storage (GCS) as a backend for Velero in the DR module configuration.
We are also introducing a new configuration option for Velero's node-agent: prepareQueueLength. This parameter controls how many backup prepare operations can be queued on a node at a given time. As a result, you can tune Velero's behavior for high-throughput backup scenarios. It can be configured via:
apiVersion: kfd.sighup.io/v1alpha2
kind: OnPremises
metadata:
name: your-cluster
spec:
distribution:
modules:
dr:
type: on-premises
velero:
nodeAgent:
prepareQueueLength: 10
...You can read the official Velero documentation for this feature here.
Security updates
Keeping your clusters secure is always a priority for us. This release includes important security updates across several components.
The auth module upgrade to v0.6.1 brings Pomerium with an updated Envoy to address the following CVEs: CVE-2025-62504, CVE-2025-62409, CVE-2025-27818, CVE-2025-27817, CVE-2025-0913, CVE-2024-25178, CVE-2024-25177, CVE-2024-25176.
The OnPremises installer update also covers CVE-2025-31133 in runc, which is a critical component of the container runtime. We strongly recommend upgrading to take advantage of this fix.
What's next?
The work on SIGHUP Distribution doesn't stop. We are already working on the next release, which will be packed with new updates.
If you have questions, feedback, or want to get involved, feel free to reach out to us or open a discussion on our GitHub repository.

